Certification Practice Statement of the Policy Authority PKIoverheid version 4.1 for G3 and G2 CA certificates v4.1
Table of Contents
- Revision history
- 1 Introduction
- 1.1 Overview
- 1.2 Document Name and Identification
- 1.3 PKI Participants
- 1.4 Certificate Usage
- 1.5 Policy Administration
- 1.6 Definitions and Acronyms
- 1.7 Guarantees (non RFC3647)
- 1.8 Verification of trustworthiness (non RFC3647)
- 1.9 Programme of Requirements and PKIoverheid Framework Council (non RFC3647)
- 2 Publication and Repository Responsibilities
- 3 Identification and Authentication
- 4 Certificate Life-Cycle Operational Requirements
- 4.1 Scope
- 4.2 Certificate Application
- 4.3 Certificate Issuance
- 4.4 Certificate Acceptance
- 4.5 Key Pair and Certificate Usage
- 4.6 Certificate Renewal
- 4.7 Certificate Re-key
- 4.8 Certificate Modification
- 4.9 Certificate Revocation and Suspension
- 4.10 Certificate Status Services
- 4.11 End of Subscription
- 4.12 Key Escrow and Key Recovery
- 4.13 Registration of certificate holders (non RFC3647)
- 5 Management, Operational, and Physical Controls
- 6 Technical Security Controls
- 6.1 Key Pair Generation and Installation
- 6.2 Private Key Protection and Cryptographic Module Engineering Controls
- 6.3
- 6.4 Other Aspects of Key Pair Management
- 6.5 Activation data
- 6.6 Computer Security Controls
- 6.7 Life Cycle Security Controls
- 6.8 Network Security Controls
- 6.9 Time-stamping
- 6.10 Cryptographic algorithms (non RFC3647)
- 7 Certificate and CRL profiles
- 8 Conformity assessment Compliance Audit and Other Assessment
- 9 Other Business and Legal Matters
- 9.1 Fees
- 9.2 Financial Responsibility
- 9.3 Confidentiality of Business Information
- 9.4 Confidentiality of Personal Information
- 9.5 Intellectual Property Rights
- 9.6 Representations and Warranties
- 9.7 Disclaimers of Warranties
- 9.8 Limitations of Liability
- 9.9 Indemnities
- 9.10 Term and Termination
- 9.11 Individual notices and communications with participants
- 9.12 Amendments
- 9.13 Dispute Resolution Provisions
- 9.14 Governing Law
- 9.16 Compliance with Applicable Law
- 9.17 Root certificate G2
- 9.18 Root certificate G3
- 10 Appendix B. Procedures for the change management of the PoR PKIoverheid
- 11 Appendix C. Certificate profile TSP CA G3
- 12 Appendix D. Content fields G2 root certificates and domain certificates
- 13 Appendix F. Content fields G3 root certificates and domain certificates
Revision history
| Version | Date of approval | Date of entry into force | Status | Author | Manager | Description |
|---|---|---|---|---|---|---|
| 3.4 | 24-06-2011 | 01-07-2011 | Adopted by the Director of Logius 24-06-2011 |
Policy Authority | H. Verweij | Editorial changes, including (but not limited to)application of RFC3647 |
| 3.5 | 29-06-2012 | 01-07-2012 | Adopted by the Director of Logius 29-06-2012 |
Policy Authority | H. Verweij | Changes in response to the Baseline Requirements of the CA/B forum and recommendations ensuing from the WebTrust audit |
| 3.6 | 04-02-2013 | 04-02-2013 | Adopted by the Ministry of the Interior and Kingdom Relations | Policy Authority | H. Verweij | The change procedure is attached as Appendix B. |
| 3.7 | 18-12-2013 | 18-12-2013 | Adopted by the Director of Logius | Policy Authority | Mark Janssen | ETSI TS 101 456 has been replaced by ETSI EN 319 411-2 Inclusion of G3 hierarchy |
| 3.8 | June 2014 | July 2014 | Adopted by the Director of Logius | Policy Authority | Mark Janssen | Paragraph layout based on RFC 3647 refined further still. Various changes made in response to the WebTrust audit. |
| 3.9 | February 2015 | February 2015 | Adopted by the Director of Logius | Policy Authority | Mark Janssen | Editorial changes + changes to the certificate profile EKU + remark concerning verification of CAA records |
| 4.0 | October 2016 | October 2016 | Adopted by the Director of Logius | Policy Authority | Mark Janssen | Replacement of ETSI TS 102 042 by ETSI EN 319 411-1 + removal of references to G1 hierarchy (expired). Also various editorial changes. |
| 4.1 | November 2016 | November 2016 | Adopted by the Director of Logius | Policy Authority | Mark Janssen | Updated section 4.2 regarding CAA issuance, specific information about CAA records is to be found in the CPS of issuing CAs. Small update to section 1.2 regarding explanation of the additional “non RFC3647” sections. English translation is now the prevailing version in case of discrepancies between Dutch and English versions of this CPS Updated references RFC2560 to RFC 6960 Updated change procedure in annex B to list possibility of changes being effective immediately after publication of a new version of the PoR. Removal of references to the G1 hierarchy and old PoR part 3b . Several small editorial changes. |
1 Introduction
1.1 Overview
1.1.1 Policy Authority for the PKI for the government
The Policy Authority of the PKI for the government (PA PKIoverheid) supports the Minister of the Interior and Kingdom Relations (MinBZK) in managing the PKI for the government.
The PKI for the government is an framework which enables generic and large-scale use of the electronic signature, and it also facilitates remote identification and confidential communication.
The tasks of the PA of PKIoverheid are:
contributing towards the development and the maintenance of the framework of standards that underlies the PKI for the government, the Programme of Requirements (PoR);
assisting in the process of admittance by Trust Service Providers (TSPs) to the PKI for the government and preparing the administration;
regulating and monitoring the activities of TSPs that issue certificates under the root of the PKI for the government.
The Policy Authority (PA) is responsible for managing the entire infrastructure. The PKI for the government is structured in such a way that external organizations, the Trust Service Providers (TSPs), can be admitted to the PKI for the government under certain conditions. Participating TSPs are responsible for the services within the PKI for the government. The PA oversees the trustworthiness of the entire PKI for the government1.
Within the scope of PKIoverheid, the PA is generally responsible for:
management of the standards system of the PKI for the government, the Programme of Requirements parts 3a through e;
management of Object Identifiers, the unique numbers for TSPs and their CPSs;
creation and management of key pair and the corresponding root certificate;
revoking the root certificate and ad-hoc publication of the CRL;
periodic publication of the CRL;
creation and management of key pairs and the corresponding domain certificates;
revocation of domain certificates and ad-hoc publication of the corresponding CRL;
preparation concerning the admission of TSPs to the PKIoverheid;
implementation of the admission of TSPs, including creation, issuance and management of TSP CA certificates;
preparation concerning the revocation of TSP CA certificates;
implementation of the revocation of TSP CA certificates;
supervision of permitted TSPs;
preparation concerning the renewal of TSP CA certificates;
implementation of the renewal of TSP CA certificates, including creation, issuance and management of new TSP CA certificates;
registration and assessment of reports regarding infringement of the PKIoverheid.
KPN BV is responsible for the technical management of Staat der NederlandenStaat der Nederlanden Root CA (G2/G3)and Staat der Nederlanden <Domain> (G2/G3) CA, the corresponding Certificate Revocation Lists (CRLs) and Online Certificate Status Protocol (OCPS) responders.
The management of root certificates and domain certificates is entrusted to the Policy Authority of the PKI for the government. This organization is part of Logius (http://www.logius.nl), digital government service of the Ministry of the Interior and Kingdom Relations.
The purpose of the Policy Authority is:
Maintaining a practicable and trustworthy framework of standards for PKI services that provides an established level of security for the government's communication needs and which is transparent for the users.
1.1.2 CA model PKIoverheid (non RFC3647)
The government's Public Key Infrastructure (PKI) has a structure consisting of a central and an operational or local level of PKIoverheid are defined; there is a structure or root based on the SHA-256 algorithm. Furthermore a division is made into different domains. Under the G2 (SHA-256) root there are domains for Organization, Citizen and Autonomous Devices. Under the G3 (SHA-256) root there are domains for Organization Person, Organization Services, Citizen and Autonomous Devices
In the past, there was also a first generation PKIoverheid root (G1), however this expired in December 2015 and will not be covered in this CPS.
The root and the domains based on the SHA-256 algorithm are denoted as G2 and G3, where the 'G' stands for generation.
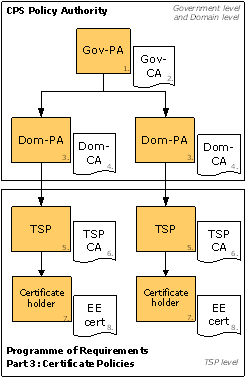
Within the central part of the PKI for the government, a number of actors are identified. These actors are (see Figure 1):
the Government PA, responsible at the highest level for laying down the policy and general standards that apply within the PKI for the government and the issue of certificates;
the Government CA, relates to a technical component that produces the highest (or root) certificate within the PKI for the government and produces certificates for the underlying domain CAs;
the Domain PA, responsible for the domain-specific content of the Government PA standards, and determines the conditions of the issue of certificates within a domain;
the Domain CA, relates to a technical component that actually produces certificates for the TSPs.
The coordinating government level and the domain level form the PKI's policy structure. Within these levels, policy and standards are laid down and the supervision is organized.
The TSP level is the operational or local part of the Public Key Infrastructure (PKI) for the government, where the direct interaction with the users takes place. At TSP level, the TSP organization is ultimately responsible for issuing certificates.
1.2 Document Name and Identification
The Certification Practice Statement within the PKI for the government (hereinafter referred to as CPS) provides TSPs, subscribers, relying parties and certificate holders2 with information regarding the procedures and measures taken in respect of the PA's services with regard to certificates. The CPS describes the processes, procedures and control measures for applying for, producing, issuing, managing and revoking certificates, insofar as the PA is directly responsible for this. This means that this CPS only relates to PKIoverheid Level 1 (Staat der NederlandenStaat der Nederlanden Root CA) and Level 2 (Staat der Nederlanden <Domain> CA).
This CPS also describes the processes and procedures for applying for, producing, issuing and revoking Level 3 <TSP name> CA certificates.
For a description of the processes, procedures and control measures for applying for, producing, issuing, managing and revoking Level 4 (end user) certificates, please refer to the relevant Certification Practice Statements of the PKIoverheid Trust Service Providers
The format of this CPS is, as far as possible, in accordance with the RFC36473 standard (in full: “Internet X.509 Public Key Infrastructure Certificate Policy and Certification Practices Framework”) of the Internet Engineering Task Force. When this CPS deviates from the RFC3647 standard this is indicated by adding ‘non RFC3647’ to the title of the segment in question. This is for specific PKIoverheid matters, which are not a part of RFC3647.
Formally, this document is referred to as the 'Certification Practice Statement certificates within the PKI for the government'.
The PA publishes two language versions of this CPS; English and Dutch. Great care is taken in ensuring parity in both language versions. In case of discrepancies between the English version and the Dutch version of this document, the English version shall prevail.
| CPS | Description |
|---|---|
| Naming | CERTIFICATION PRACTICE STATEMENT (CPS) Policy Authority PKIoverheid for certificates to be issued by the Policy Authority of the PKI for the government |
| Link | https://cps.pkioverheid.nl |
| OID | N/A |
Public information about the PA or the PKI for the government is available at http://www.logius.nl/pkioverheid.
1.2.1 Objective of CPS (non RFC3647)
This CPS provides information to TSPs, subscribers, relying parties and certificate holders regarding the procedures and measures taken with regard to the PA's services. The quality of the services underpins the trust that can be placed in the PKI for the government. In this respect, the relationship between the PA and Trust Service Providers (TSPs) is also of importance. This relationship and the conditions under which TSPs can participate in the PKI for the government are broadly described. TSPs interested in participating in the PKI for the government can obtain more detailed information about this subject from the PKIoverheid Programme of Requirements part 2.
1.2.2 Relationship between CPS and CP (non RFC3647)
The CP PoR parts 3a through e describe the minimum requirements stipulated in relation to the services of a TSP within PKIoverheid. This CPS states how the PKIoverheid services will be put into practice, insofar as this is under the direct responsibility of the PA.
1.2.3 CA/Browser Forum Baseline Requirements (non RFC3647)
The PA of PKIoverheid conforms to the current version of the Baseline Requirements for Issuance and Management of Publicly-Trusted Certificates as published at http://www.cabforum.org. In the event of any inconsistencies between the PKIoverheid Programme of Requirements parts 3e [2.16.528.1.1003.1.2.5.6] and the relevant Requirements, causing the inability to fulfil the minimum requirements put forth herein, the provisions in the Baseline Requirements shall prevail.”
1.2.4 Certificate Policies (CPs) (non RFC3647)
This part relates to the requirements laid down for the services of a Trust Service Provider (TSP). Nine areas are identified, each of which are covered in a separate part, which are:
Part 3a – Certificate Policy for Organization and Organization Person Domain;
Part 3b – Certificate Policy for Organization and Organization Services Domain;
Part 3c – Certificate Policy for Citizen Domain;
Part 3d – Certificate Policy for Autonomous Devices Domain;
Part 3e – Certificate Policy for Server Certificates.
Part 3f – Certificate Policy for Extended Validation
Part 3g – Certificate Policy for Private Services
Part 3h – Certificate Policy for Private server certificates
Part 3i – Certificate Policy for Private Persons
This CPS only relates to CP parts 3a through 3e. The “CPS Policy Authority PKIoverheid for Extended Validation certificates to be issued by the Policy Authority of the PKI for the government" relates to CP part 3f.The”CPS Policy Authority PKIoverheid for Private Root
certificates to be issued by the Policy Authority of the PKI for the government” relates to CP parts 3g through 3i.
1.2.4.1 Positioning Programme of Requirements (non RFC3647)
The Programme of Requirements forms the basis of the PA's services. Laid down in the Programme of Requirements are the requirements for the PKI for the government; these requirements are derived from international standards and the applicable legislation. The Programme of Requirements is made up of four parts and in each part, a specific aspect of the PKI for the government is elaborated on in further detail.
1.2.4.2 Introduction Programme of Requirements (non RFC3647)
This part includes an introduction to the Programme of Requirements and the PKI for the government.
1.2.4.3 Admittance and supervision (non RFC3647)
Part 2 describes how a TSP can be admitted to the PKI for the government, can demonstrate compliance with the requirements and which formalities have to be met. It also describes how the PA regulates the TSPs that have been admitted.
1.3 PKI Participants
In this CPS, six parties are identified, each with their own responsibility within the PKI for the government . Consecutively, these parties are:
the Ministry of the Interior and Kingdom Relations;
the Policy Authority (PA);
the Trust Service Provider (TSP);
Subscriber;
Certificate holder;
the relying party.
The responsibilities and the corresponding activities for each of these parties are briefly described below.
The Ministry of the Interior and Kingdom Relations is responsible for the PKI for the government. The Ministry of the Interior and Kingdom Relations makes decisions regarding the layout of the infrastructure and the participation of TSPs in the PKI for the government. The director of Logius represents the Ministry of the Interior and Kingdom Relations in this matter.
The PA advises the director of Logius and is responsible for managing the central part4 of the PKI for the government and supervising and monitoring the work of TSPs that issue certificates under the Staat der Nederlanden Root CA of the PKI for the government.
One or more TSPs operate in each domain of the PKI for the government. Within a domain of the PKI for the government, a TSP will issue certificates to the certificate holders. The obligations of the TSPs that form part of the PKI for the government are defined in the Programme of Requirements, parts 3a through 3e: Certificate Policies.
A subscriber enters into an agreement with a TSP on behalf of one or more certificate holders. How the delivery of certificates takes place is organized between the subscriber and the TSP.
The certificate holder is the holder of the private key belonging to the public key contained in the certificate. Certificate holders can be found at all levels in the hierarchy of the PKI for the government. End users receive the certificates from the TSPs. The PA issues certificates to itself (Staat der Nederlanden Root CA and Staat der Nederlanden <Domain> CAs) and to TSPs (TSP CA).
The relying party is the recipient of a certificate issued within the PKI for the government and acts on the basis of trust inthe certificate. The relying party is obliged to check the validity of the full chain of certificates through to the source (root certificate) on which trust is placed. This obligation is included in the Programme of Requirements, part 3: Certificate Policies.
1.4 Certificate Usage
Within the PKI for the government, different types of certificates are defined at four levels, which are:
Root certificate;
Domain certificate;
TSP certificate;
End user certificate.
The root certificate, the domain certificates and the TSP certificates can only be used to verify the issuer's signature and are issued by the Policy Authority. These certificates may not be used for other purposes. The TSPs. End user certificates can be used for authenticity, non-repudiation, confidentiality and a combination of authenticity and confidentiality issues the end user certificate.
This CPS relates to the trustworthiness of the Policy Authority's services, therefore this paragraph only covers the procedures relating to root, domain and TSP certificates.
1.5 Policy Administration
1.5.1 Organization responsible for managing the CPS
The Ministry of the Interior and Kingdom Relations is responsible for this CPS. The Ministry has delegated this task to Logius. This also includes the approval of changes to this CPS.
1.5.2 Contact information
Should there be any complaints, questions or alerts, TSPs within the PKIoverheid framework can contact staff of the PA PKIoverheid through the usual channels. The PA PKIoverheid is available during office hours and will respond as quickly as possible. In the event of reports of incidents or emergencies outside of office hours, the Logius Service Centre should be contacted, which is available 24 hours a day.
Subscribers who have questions concerning the issuance of certificates are asked to initially contact their (potential) TSP.
Other involved parties can contact the Logius Service Centre. The service centre registers the question and will answer this within the stipulated period of time. If necessary, questions asked through the service centre are forwarded to the PA PKIoverheid, or in the event of an incident, to the on-duty incident manager.
Contact information
Policy Authority PKIoverheid
Wilhelmina van Pruisenweg 52
P.O. Box 96810
2509 JE THE HAGUE
http://www.logius.nl/pkioverheid
General telephone number: +31(0)708896360
Email: servicecentrum@logius.nl
1.5.3 The person who verifies the eligibility of CPS for the CP
The PA PKIoverheid does not have its own Certificate Policy. Approval of the CPS is discussed in 1.5.4.
1.5.4 Change procedure CPS
The PA of PKIoverheid is entitled to change or to add to this CPS. Changes apply as from the time that the new CPS is published, in accordance with the provisions in paragraph 9.10. The management of Logius is responsible for observing the procedure described in paragraph 9.12 accurately and for the ultimate approval of this CPS in accordance with this procedure.
1.6 Definitions and Acronyms
In part 4 of the PoR, an explanation is given regarding the definitions and acronyms used in the Programme of Requirements.
For a list of the used definitions and acronyms, please refer to http://www.logius.nl/begrippenlijst (in Dutch).
1.7 Guarantees (non RFC3647)
When issuing PKIoverheid certificates, the following parties are recognised:
Subscriber;
End user;
Organizations that develop internet browser software;
Relying parties.
These parties are informed that:
The PA of PKIoverheid guarantees that sub-CAs within the PKIoverheid framework are known to the PA and remain under the control of the TSP that has created a sub-CA. In addition these sub-CAs shall not be used for man-in-the middle (MITM)purposes.
All sub-CA certificates issued within the PKI for the government are listed on this website:
PKIoverheid and its Trust Service Providers guarantee that, , when a PKIoverheid services - server certificate is issued, they have adhered to the requirements from the CA/Browser Forum Baseline Requirements and the PoR parts 3b and 3e [2.16.528.1.1003.1.2.2.6 and 2.16.528.1.1003.1.2.5.6] and that they checked the information included in the services - server certificate for accuracy and completeness.
For a description of the safeguards, please refer to the relevant Certification Practice Statements of the PKIoverheid Trust Service Providers.
1.8 Verification of trustworthiness (non RFC3647)
In figure 2, the structure is presented from the point of view of the relying parties. A relying party has a certificate (4) of another party (the certificate holder) and requires certainty regarding the trustworthiness of this certificate. A certificate is verified by performing the following checks 5:
Has the message been changed whilst being sent, (e.g. is the integrity safeguarded?)
Has the certificate that has been used been revoked and included on a so-called "black list"?
Is the certificate still valid?
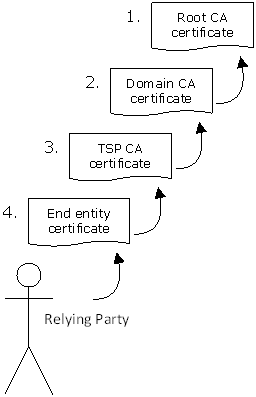
The software then establishes whether the certificate has been issued by a trusted party. To be able to perform this final verification, the software has to have the root certificate of the PKI for the government. If the root certificate is not available, the user receives an error message. That is why the PA has decided to include the root certificate in frequently used operating systems and (Open Source) browsers.
When software is used in which the root certificate is not included, the relying party can securely download the root certificate at https://cert.pkioverheid.nl
The TSP certificate (3) is issued by the PA and can be verified using the domain certificate (2). This latter certificate is also issued by the PA and can be verified using the root certificate (1). At each level of the PKI for the government, the trust in a certificate therefore depends on the trust placed in the party that has issued the certificate. From a relying party's point of view, this is the TSP for the first verification step, the PA for the second step at domain level and finally the PA at the highest level of the hierarchy. The root certificate is therefore the pivotal point of trust in the hierarchy of the PKI for the government and determines the trust placed in all other certificates issued within the PKI for the government. By expressing the trust in the root certificate, all underlying domain, TSP and end user certificates are trusted. The users only have to trust one certificate.An important aspect is determining the trustworthiness of the government body that issues the certificate.
1.8.1 Trustworthiness of the issuing government body (non RFC3647)
To be able to trust a certificate, the relying party has to determine whether it wishes to place trust in the issuing government body (the TSP). The relying party can do this by assessing the Certification Practice Statement (CPS) of the TSP. The certificate contains a reference to the CPS. To avoid a relying party having to assess every CPS of the TSPs within the PKI for the government in detail, the hierarchy of the PKI for the government was created. The conditions for issuance, management and also the use of end user certificates are described by the PA in the so-called CP. The CP is therefore key to the CPS of the various TSPs active within the PKI for the government.
For there to be a trustworthy hierarchy, it is therefore very important that the PA operates in a trustworthy manner. The PA safeguards the trustworthiness of the root certificate and the domain certificates by applying effective security measures. These security measures, as well as the way in which the PA regulates the TSPs, are described in this CPS of the PA. By assessing the CPS of the PA, the relying party can determine whether they trust a certificate that is issued within the hierarchy of the PKI for the government. In addition, the trustworthy operation of the PA is ratified periodically by an audit being performed by external auditors.
1.9 Programme of Requirements and PKIoverheid Framework Council (non RFC3647)
The Programme of Requirements is the formal framework of standards in respect of the trustworthiness and quality of services within the PKI for the government. While the PA maintains these standards, it is important that the practical experiences and ideas of users are also taken into account. To be able to generate this support for the use of the Programme of Requirements, a PKIoverheid Framework Council has been set up that is consulted regarding decision-making about change proposals in respect of the Programme of Requirements . The Council also discusses subjects that are generally relevant to the PKI developments.
The full set of procedures for the change control of the Programme of Requirements of PKIoverheid are attached as Annex B.
2 Publication and Repository Responsibilities
2.1 Electronic repository
The PA publishes the root certificate, the domain certificates and the TSP certificates on its website (https://www.pkioverheid.nl). Also available on the website is information regarding the use of the root certificate, the domain certificates and the TSP certificates and CRLs for the Domain and TSP CA certificates.
An admitted TSP publishes the TSP certificates issued by the PA on its own website. A reference is also included to the root certificate and the domain certificates on the PA's website.
The CRLs relating to the end user certificates can be found on the websites of the various TSPs.
2.2 Publication certificate information
The following certificates are published:
Staat der Nederlanden Root CA – G2;
Staat der Nederlanden Burger CA – G2;
Staat der Nederlanden Organisatie CA – G2;
Staat der Nederlanden Autonome Apparaten CA - G2;
Staat der Nederlanden Root CA – G3;
Staat der Nederlanden Burger CA – G3;
Staat der Nederlanden Organisatie Services CA – G3;
Staat der Nederlanden Organisatie Persoon CA – G3;
Staat der Nederlanden Autonome Apparaten CA – G3;
<Name TSP> CA – G2;
<Name TSP> CA – G3.
This CPS can be found at the following URL:
The following CRLs are published. These can also be found on the website https://crl.pkioverheid.nl. Below are the direct links to the CRLs:
For revoked State of the Netherlands CA domain certificates:
http://crl.pkioverheid.nl/RootLatestCRL-G2.crl
http://crl.pkioverheid.nl/RootLatestCRL-G3.crlFor revoked TSP CA certificates:
http://crl.pkioverheid.nl/DomOrganisatieLatestCRL-G2.crl
http://crl.pkioverheid.nl/DomBurgerLatestCRL-G2.crl
http://crl.pkioverheid.nl/DomAutonomeApparatenLatestCRL-G2.crlhttp://crl.pkioverheid.nl/DomOrganisatieServicesLatestCRL-G3.crl
http://crl.pkioverheid.nl/DomOrganisatiePersoonLatestCRL-G3.crl
http://crl.pkioverheid.nl/DomBurgerLatestCRL-G3.crl
http://crl.pkioverheid.nl/DomAutonomeApparatenLatestCRL-G3.crl
2.2.1 Official electronic notification (non RFC3647)
The attributes of the root certificates are published in the Official Gazette (Staatscourant) and attached as Appendix A
G2: published in the Official Gazette (Staatscourant) dated 15 December 2008 (no. 243, page 1);
G3: published in the Official Gazette (Staatscourant) dated 10 April 2014 (no. 10020, page 1).
2.2.2 Distribution Public Key (non RFC3647)
The public key of the root certificate is distributed through the trusted root certificate programmes of various software suppliers. An up-to-date list of the software products containing the PKIoverheid root certificate can be found at https://www.logius.nl/ondersteuning/pkioverheid/browserondersteuning-pkioverheid/.
The root certificate is also provided in a trustworthy manner at https://cert.pkioverheid.nl .
2.3 Frequency of Publication
The information in the electronic repository will be published or updated as quickly as possible. When a new version of the CPS is published, the TSPs participating in the PKIoverheid framework will be informed by email.
The PA publishes the lists of revoked certificates, the Certificate Revocation Lists (CRLs). There is a CRL with revoked domain certificates. This CRL is republished annually. This CRL is published ad-hoc after revocation of a domain certificate. For each domain, there is a CRL with revoked TSP certificates within that domain. A domain CRL is republished every six months. A domain CRL is published ad-hoc after revocation of a TSP certificate.
Each CRL contains the time of the next planned CRL release. These CRLs can be found at: https://crl.pkioverheid.nl.
As well as the publication of the CRL, the PA also offers status information for the Organization Services domain through the Online Certificate Status Protocol (OCSP). To this end, the following two OCSP have been set up.
http://RootOCSP-G3.OCSP.pkioverheid.nl provides status information about the Organization Services domain certificate;
http://DomOrganisatieServicesOCSP-G3.OCSP.pkioverheid.nl provides status information about the TSP certificates in the Organization Services domain.
The OCSP responders conform to RFC69606.
2.4 Access to publication
Published information is public in nature and freely accessible. The Electronic Repository can be accessed twenty-four hours a day, seven days a week. The Electronic Repository is protected against unauthorised changes being made.
In the event of system failure or other factors that have a negative impact on the availability of the Electronic Repository, an appropriate set of continuity measures have been prepared to ensure that the CRL will be available again within 4 hours and the other parts of the Electronic Repository within 24 hours. An example of such a measure is having created a fall-back facility and scenario. In addition, every year the repository will undergo a penetration test. This is carried out by an external IT security company.
3 Identification and Authentication
3.1 Naming
3.1.1 Types of names
All certificates issued by the PA of PKIoverheid contain a 'subject' field (DistinguishedName) which lists the name of the holder. The names used in the certificates fulfil the X.501 name standard. The names consist of the following components:
| Attribute | Staat der Nederlanden Root CA – G2 | Staat der Nederlanden <Domain> CA – G2 | <TSP name> CA – G2 |
|---|---|---|---|
| Country (C) | NL | NL | NL |
| Organization (O) | Staat der Nederlanden | Staat der Nederlanden | <TSP Organization name> |
| CommonName (CN) | Staat der Nederlanden Root CA-G2 | Staat der Nederlanden <domain> CA – G2 | <TSP name> <domain> CA – G2 |
| Attribute | Staat der Nederlanden Root CA – G3 | Staat der Nederlanden <Domain> CA – G3 | <TSP name> PKIoverheid <domain> CA – G3 |
|---|---|---|---|
| Country (C) | NL | NL | NL |
| Organization (O) | Staat der Nederlanden | Staat der Nederlanden | <TSP Organization name> |
| CommonName (CN) | Staat der Nederlanden Root CA – G3 | Staat der Nederlanden <domain> CA – G3 | <TSP name> PKIoverheid <domain> CA – G3 |
| OrganizationIdentifier | The format of the identification string is specified in paragraph 5.1.4 of ETSI EN 319 412-1 and includes:
|
For other provisions regarding the way in which identification and authentication take place within PKIoverheid, please refer to the relevant Certification Practice Statements of the PKIoverheid Trust Service Providers.
3.1.2 Need for names to be meaningful
There are no other provisions in this respect for the certificate services by the PA.
3.1.3 Pseudonyms
The use of pseudonyms or anonymous certificates is not permitted.
3.1.4 Rules for interpreting various name forms
The name of the TSP CA is copied from the extract in the Dutch Trade Register.
3.1.5 Uniqueness of names
All certificates issued under this CPS, contain a unique subject field (DistinguishedName).
3.1.6 Recognition, authentication and role of trademarks
The PA assumes the correctness of the name of organizations as listed in the Dutch Trade Register of the Chamber of Commerce.
3.2 Initial Identity Validation
3.2.1 Initial Registration Process
For the requirements laid down in relation to the initial registration process, see the PKIoverheid Programme of Requirements, part 2.
3.2.2 Authentication of organizational identity
Based on the application form and the evidence that is supplied, the PA verifies,
that the TSP is an existing organization listed in the National Trade Register (NHR) or an organisational entity that forms part of an existing organization listed in the NHR. If a government organization is not listed in the NHR, the State Almanac is consulted;
that the name of the organization and country name registered by the TSP to be incorporated in the certificate are correct and complete and that the applicant is authorised to represent the organization;
the presence of the relevant registration information of the prospective TSP, with the corresponding evidence (excerpt from the Chamber of Commerce, etc.). The excerpt must be original and must not be older than 13 months.
Note: If the participating party has existed for less than three years and does not appear in the latest version of the quoted registration sources, the identity and validity of the prospective TSP can be, if required, established using a parent company or parent ministry that are registered in the NHR or the State Almanac.
3.2.3 Authentication of individual identity
Upon initial admittance to the PKIoverheid framework, the PA verifies the listed personal data of the authorised representative of the TSP using an identity document issued under art. 1 of the Compulsory Identification Act:
a valid travel document referred to in the Passport Act (Paspoortwet);
a valid driving licence issued on the basis of the Road Traffic Act (Wegenverkeerswet), under article 107 of the Road Traffic Act (Wegenverkeerswet) 1994.
3.3 Identification and Authentication for Re-key Requests
Often, a TSP has already been admitted to PKIoverheid when a new TSP CA has to be created under a new generation of the regular root. It is also possible that a TSP that has already been admitted wishes to issue certificates under a new domain or a different root. In that case, a abbreviated procedure can be applied for the identification validation, because the TSP CA is already known to the PA and has been admitted to PKIoverheid.
It is then sufficient for the PA to verify whether the organization name and name of the country provided in the Naming document/CSR is still correct. This can be verified as follows:
By online consultation of the NHR to verify whether the TSP CA is an existing organization;
By online consultation of a database such as Dunn & Bradstreet, which is kept up-to-date and which is considered to be a trustworthy source.
In addition, the PA must verify that the application came from the actual TSP CA. An application can be submitted in two ways:
The authorised representative can send an application form by email and sign this using a PKIoverheid certificate;
The authorised representative can sign an application form and send this by post.
In the second case, the registered authorised representative of the TSP CA should also be contacted by the PA to verify the application. For purposes of verification, identifying details of the contact person or organization can be requested.
This identification verification by the PA is recorded and archived in the TSP CA file.
3.4 Identification and Authentication for Revocation Requests
A request for revocation of a certificate can be submitted by the TSP CA. When a request for revocation is made, the reasons for this must always be given. In consultation with the parties involved, it will be examined to what extent the request can be complied with, as revocation of a TSP CA means that the underlying certificates will no longer be valid.
Identification and authentication of the party submitting the request to revoke the TSP CA can take place as follows:
A request by email to the PA, where the request is signed digitally with a qualified electronic signature;
A request by signed letter;
In both cases, the PA will contact the authorised representative of the TSP CA by telephone to establish whether the request for revocation is genuine. For purposes of verification, identifying details of the contact person or organization can be requested.
4 Certificate Life-Cycle Operational Requirements
4.1 Scope
Within the PKI for the government, different types of certificates are defined at four levels, which are:
Root certificate;
Domain certificate;
TSP certificate;
End user certificate.
The root certificate, the domain certificates and the TSP certificates can only be used to verify the issuer's signature and are issued by the Policy Authority. These certificates may not be used for other purposes. The end user certificate is issued by the TSPs.
This CPS relates to the trustworthiness of the Policy Authority's services, therefore this paragraph only covers the procedures relating to root, domain and TSP certificates.
4.2 Certificate Application
The root certificate, the domain certificates and TSP certificates are created by the Policy Authority, at the instruction of the Ministry of the Interior and Kingdom Relations.
The instruction to create TSP CA certificates is by means of a request to this end by a TSP. For more information, see PKIoverheid PoR part 2.
When TSP CAs are signed, the PA PKIoverheid does not verify CAA records.
Within the PKIoverheid hierarchy a domain holder can indicate which TSP (issuing CA) may issue a TLS (EV) certificate by adding a CAA issue record in the DNS entry of that domain. A CAA issue record with the value “www.pkioverheid.nl” permits issuance by all TSPs that issue PKIoverheid TLS (EV) certificates. Alternatively a domain holder can limit issuance to a particular TSP by using its specific CAA identifier, which can be found in the CPS document of that TSP.
4.2.1 Methodology with regard to creating certificates
The root certificate, the domain certificates and TSP certificates are created during special creation ceremonies. A certified external IT auditor acts as witness during the creation ceremonies of the Staat der Nederlanden Root CA and Staat der Nederlanden <Domain> CA. A certified external IT auditor is also present as witness during the creation of the TSP CAs. For every creation ceremony, a detailed script is produced which lists all tasks to be carried out. This main purpose of this script is to prevent any input errors during the ceremony. A creation ceremony takes place in accordance with the script in the presence of independent witnesses. The identity of the persons present is verified using the valid documents referred to under article 1 of the Compulsory Identification Act (“Wet op de identificatieplicht”).
The creation ceremonies take place in a similar manner for all of the listed types of certificates, where the certificate holder is either the PA or the TSP. During the ceremony, the following steps take place:
building the computer system;
installing and configuring the PKI software;
activating the Hardware Security Module (HSM), where several keyholders each introduce part of the activation data;
generating the key pairs;
generating certificates for each key pair;
dismantling the computer system and
securing the computer system and the critical components.
4.3 Certificate Issuance
The requirements which a TSP must fulfil when issuing the certificates are formulated in part 3 (Certificate Policies) of the Programme of Requirements. The way in which a TSP implements these requirements must be defined by the TSP itself in a Certification Practice Statement (CPS). The description of the services by TSPs therefore falls outside the scope of the specification of this CPS.
There is no separate CP for the issuance of certificates by the PA, as the PA does not issue end user certificates. The measures that the PA has taken to guarantee the trustworthiness of the certificates to be issued by the PA are described in this CPS.
4.4 Certificate Acceptance
The script associated with the creation ceremonies also contains the procedure for ascertaining the accuracy and accepting the certificates that are created. Also listed in the script are the names of the people involved. The PA establishes the accuracy of the certificates. The TSP then accepts the TSP certificates.
4.5 Key Pair and Certificate Usage
The Staat der Nederlanden Root CA, Staat der Nederlanden <Domain> CAs and the TSP CAs certificates are primarily used to verify the issuer's signature and are issued by the PA. These certificates are also used for CRL signing. These certificates may not be used for other purposes. The end user certificate is issued by the TSPs.
4.6 Certificate Renewal
Certificates have to be renewed when (part of) the information that forms the basis of the certificate changes or is out of date. For example, if the name of a TSP as included in the certificate changes or if the strength of a cryptographic algorithm is deemed insufficient and a stronger cryptographic algorithm is included.
Certificate Renewal where the existing key pair is maintained and the maximum lifetime of a certificate is extended is not applied within PKIoverheid.
The time of (routine) renewal of certificates is related to the lifecycle of certificates and signing keys. For the relying party, during the term of an end user certificate, it must also be possible to verify the validity of the certificate. When an end user certificate is verified, the validity of the aforementioned certificates of issuing TSPs is also verified. Therefore the TSP certificate, the domain certificate and the root certificate will have to be valid during the course of the validity period of an end user certificate.
Once every five years, the PA will generate new signing keys (for root and domains) and issue new certificates (root certificate and domain certificates). The new signing keys replace the previous versions; the original certificates will continue to exist alongside the new certificates. The original certificates can be used to verify certificates that are issued under the original root.
The signing keys of a TSP have to be renewed at the time at which the lifespan of the parent certificate (TSP certificate, domain certificate or root certificate) expires, minus the term of validity of the end user certificate. Taking this required verification period into account, a TSP has to create new signing keys (or arrange for these to be created) and also submit a request to the PA to create the new TSP certificate.
This request is the first step of the internal procedure of TSP certificate renewal. This procedure broadly comprises the following steps:
Submission of an application form to renew a TSP CA under the new root by the authorised representative of the TSP;
Verification of the validity of the request by the PA;
Validation of the data in the application form;
Submission of the Naming Document for the new TSP CA certificate by the TSP;
Verification of the Naming Document by the PA;
Submission of the Certificate Signing Request (CSR) by TSP for Test TSP CA;
Creation of a Test TSP CA certificate by the technical administrator of the root;
Verification Test of TSP CA certificate by the PA and TSP;
Submission of a Certificate Signing Request (CSR) by TSP for Production TSP CA;
Instruction from the PA to the technical administrator of the root for the creation of a new TSP CA certificate;
Execution of a creation ceremony of new TSP CA certificate by the technical administrator of the root;
Verification by PA of new TSP CA certificate;
Handover by PA of new TSP CA certificate to the TSP;
Discharge of the technical administrator of the root by PA.
The request, the issuance, the adoption and the publication of the new TSP certificate follow the same steps as those taken for the original admittance of a TSP, see 4.2 to 4.5. The new signing keys replace the previous versions. The original TSP CA certificate will continue to exist for a certain period of time alongside the new TSP CA certificate.
The original certificates can be used for verification of certificates that are issued under the original TSP certificate.
4.7 Certificate Re-key
Certificate Re-key where the existing public key of a certificate is changed, is not applied within the central hierarchy of the PKI for the government.
4.8 Certificate Modification
Certificate Modification is only applied in exceptional cases. Usually, the preference is to reissue a certificate when the content of the certificate (public key) is no longer correct.
4.9 Certificate Revocation and Suspension
Revocation of the root certificate, a domain certificate or a TSP certificate will in any cases be considered if the signing key belonging to the certificate is compromised or suspected to be compromised. The TSP is considered to be compromised if unauthorised access is gained to this signing key or when carriers of the private key are stolen or lost. To effect this, the PA keeps records of incidents that can lead to revocation of the root certificate, a domain certificate or a TSP certificate. All messages are registered by the PA and are dealt with. The Personal Data Protection Act (“Wet Bescherming Persoonsgegevens”) applies and is taken into account.
The PA considers compromise of the signing key to be an emergency. Should an emergency occur, the emergency plan will take effect and all relevant parties will immediately be informed. The emergency plan is discussed in paragraph 5.7 of this CPS.
Prior to revocation of a root certificate, a domain certificate or a TSP certificate and the keys associated with this certificate, a careful assessment process is followed. The emergency team will perform this assessment and will initiate any activities that may ensue from this, or arrange for these to be initiated.
If a TSP no longer fulfils the conditions for participation in the PKI for the government, the PA can revoke the relevant TSP certificate. The revocation of a certificate can be effectuated within one day. The PA informs the TSP prior to the certificate being revoked.
If the root certificate is revoked, the PA informs the TSPs. The revocation of the root certificate is reported in the Official Gazette (Staatscourant) and through other media where the root certificate is or shall be formally published.
In the event of the revocation of a domain certificate, the PA can inform the child CAs (TSPs).
The decision to revoke the root certificate or a domain certificate will be accompanied by a decision on whether or not a new certificate will be issued to replace the revoked certificate.
The revocation of a domain certificate or a TSP certificate always leads to ad-hoc publication of the relevant modified CRL. The revocation of certificates and the issue of CRLs takes place in accordance with a pre-prepared script. The new CRL will be published a maximum of 24 hours after revocation of a domain or TSP CA..
Certificate suspension is notsupported within the PKI for the government.
4.10 Certificate Status Services
4.10.1 Operational characteristics of the Certificate Status Service
The validity of certificates can be consulted using the published CRL which is available through the electronic repository (see 2.1). For the CRLs, the PA uses the X.509 version 2 format.
As well as the publication of the CRL, the PA also offers an Online Certificate Status Protocol (OCSP) service for the G3 root certificate and the G3 domain organization services. The OCSP service is normally updated every 12 hours. An OCSP response from this service remains valid for up to 7 days. In the event of the revocation of a G3 TSP CA certificate, the OCSP service is updated ad-hoc. The OCSP service supports the GET method for requesting a response.
With regard to its CRL and OCSP services, the TSP retains appropriate server capacity, meaning a response time will be guaranteed of 10 seconds or less under normal circumstances.
During the lifetime of the aforementioned CA, the status of revoked certificates will remain available on the CRL and through OCSP.
4.10.2 Certificate Status Service availability
The CRL and OCSP are available 24 hours a day, 7 days a week.
The maximum period of time within which the availability of the revocation status information (the status of a revoked certificate) has to be restored is four hours.
4.10.3 Optional attributes of the certificate status service
No further provisions for the certificate services of TSP.
4.11 End of Subscription
If the Ministry of the Interior and Kingdom Relations decides to end the PKIoverheid service, the following actions will be undertaken:
All involved parties (subscribers, cross-certifying CAs, parent CAs and relying parties) of the PKIoverheid service shall be informed six months before the service ends.
All certificates that are issued after announcement of termination of the service has been communicated shall contain a termination date which is the same as the planned termination date of PKIoverheid.
When the service ends, all certificates that are still valid shall be revoked.
On the termination date, PKIoverheid ceases to distribute certificates and CRLs.
4.11.1 Transfer of PKIoverheid (non RFC3647)
If the Ministry of the Interior and Kingdom Relations decides to transfer the PKIoverheid service to a different organization, all involved parties (subscribers, cross-certifying CAs, parent CAs and relying parties) of the PKIoverheid service will be informed of this transfer at least 3 months in advance. The new organization will transfer the provisions from this CPS to its own CPS.
4.12 Key Escrow and Key Recovery
The PA PKIoverheid has cloned the root and domain certificates and this back-up is saved at the back-up site of PKIoverheid.
4.13 Registration of certificate holders (non RFC3647)
Unlike the TSP, the PA does not issue certificates to natural persons. A register with the personal data of certificate holders is therefore not available.
5 Management, Operational, and Physical Controls
This CPS contains a high-level description of the security measures taken by the PA.
The PA has implemented control measures in order to prevent loss, theft, damage or compromise of infrastructural assets and disruption of activities. Physical access control is among these measures. The physical set-up is made up of various layers which require separate access control, each layer requiring a higher level of security. A series of measures have also been taken to protect against fire, natural disasters, failure of supporting facilities (such as electricity and telecommunication facilities), the risk of collapse, leakages, etc.
5.1 Physical Security Controls
The secured environment of the root of the PKI for the government is set up based on the requirements formulated in the WebTrust Program for Certification Authorities, and the Civil Service Information Security (Classified Information) Decree (Voorschrift Informatiebeveiliging Rijksdienst voor Bijzondere Informatie) (VIR-BI).
5.2 Procedural Controls
Specific processes and procedures have been implemented to handle incidents and emergencies,.
The Policy Authority performs a system-wide risk analysis annually and describes the control measures taken to mitigate the risks within the system. A risk analysis is also performed when there are significant changes in internal or external factors.
In addition, every year a risk analysis is performed on the technical management of the central hierarchy of PKIoverheid.
The computer systems for production are not used for other purposes. , For the testing or acceptance of new or modified software separate systems have been set up. Apart from this separation of hardware, procedures are in force that ensure that all employees respect the principle of a strict separation between the acceptance and the production environment.
The responsibilities of the PA are allocated between different functions and persons. The software checks the segregation of duties and enforces this. Generally, it is ensured that the implementation of security tasks and of regulation and verification take place independently of the implementation of production tasks. More PKI-specific measures are taken in respect of producing the key material and certificates. The PA can only generate key material and certificates in the simultaneous presence of various key holders. Each key holder only has access to part of the activation data that is required to be able to use the signing key. When producing and publishing CRLs, this so-called N out of M principle is also applied7. Other conditions are:
The CA systems are stand-alone systems, without external network links;
During operational use, CA systems are situated in a secure room that can only be accessed by persons authorised to do so;
After use, the CA system along with all peripheral equipment and key parts are stored in a safe that is located in the aforementioned secure room;
The CA systems are operated by a key manager, who works strictly according to the scripts and under the constant observation of a witness. Depending on the ceremony, this is an independent external witness or a representative of the PA. Any deviations from the script will be meticulously recorded;
From the very start (retrieving CA systems and key parts) to the end (compressing CA systems and key parts), the entire ceremony is recorded and saved. The recordings are stored.
During the ceremony, the partial keys are in the possession of the relevant key holders. The distribution of the partial keys between the key carriers is such that a specific activity cannot be carried out by the technical administrator without at least 2 civil servants being present. The N out of M principle means that several partial keys and key carriers are required.
A request for certification (signing) is presented by the PA to the technical administrator.
5.3 Personnel Security Controls
The PA shall ensure that trusted personnel have no conflicting interests, in order to safeguard the impartiality of the activities of the PA. If this is considered necessary, the PA will only take on people in positions of trust when, based on security screening level B performed by the General Intelligence and Security Service (AIVD), a statement of no objection is issued.
The PA employs personnel who have the required expertise, experience and qualifications for the relevant positions.
5.4 Audit Logging Procedures
For the purpose of auditing, the PA records computer loggings on the changes in the systems that form part of the technical infrastructure of the top of the hierarchy and that are of importance for the trustworthiness of the services. Examples of this are creating accounts, installation of software, back-ups, closing and (re)starting the system, hardware changes and securing audit-log files.
All activities of the PA relating to generating keys and producing certificates and CRLs are logged in such a way that retrospective reconstruction of the system operations is possible.
During a TSP ceremony, when starting up the information systems, it is checked whether (unauthorised) changes have been made to these.
After each ceremony, a full back-up is made of the system and database. The back-ups are stored for a minimum period of 7 years. This only applies to the last two images from the system.
5.5 Records Archival
The PA archives relevant records relating to certificates issued by the PA, for a period of at least thirty years. This includes the documents relating to procedures carried out when creating and revoking the certificates and documents/files required in order to ascertain the validity of root certificate, domain certificates or TSP certificates at a specific point in time. The archived documents are stored by the PA in a secure manner.
The public keys of the root certificate, the domain certificates and the CRL certificates are archived as part of the corresponding certificates.
Once the validity of the TSP certificate has expired, the PA shall save, for a period of at least 7 years, all information relating to the application and revocation, if applicable, of the TSP certificate and all information used to verify the identity of the TSP, the Authorized Representative and the certificate manager.
5.6 Key Changeover
Keys of certificate holders may not be reused once the term of validity has expired, or once the corresponding certificate has been revoked. When certificates are renewed, the key pair is also renewed.
5.7 Compromise and Disaster Recovery
The PA puts provisions in place to safeguard the continuity of its services in such a way that possible disruptions are kept to a minimum. This includes maintaining critical services, including offering the revocation management service, the revocation status service and providing certificate status information through the usual channels.
The provisions that the PA has put into place include the use of redundant systems, Intrusion Detection Systems and back-ups.
In anticipation of potential emergencies that may arise within the PKI for the government, the PA has prepared an emergency plan. Described in this plan are the measures to resolve an emergency as quickly as possible. The emergency plan therefore outlines how an emergency team will immediately be convened, with certain authorities and resources, which will take appropriate action.
Several parties are active within the PKI for the government (Ministry of the Interior and Kingdom Relations, PA, TSPs and the technical administrator of the root). Any of these parties can suffer an emergency, potentially impacting the other parts of the PKIoverheid chain. To be able to act in a coordinated manner in the event of an emergency, the emergency plans of the various parties are coordinated with one another.
To be properly prepared for potential emergencies and to limit the impact of an emergency the PA's emergency plan is tested periodically, at least once a year. The coordination and communication with the involved parties from the PKIoverheid chain are then also tested.
6 Technical Security Controls
6.1 Key Pair Generation and Installation
The key pairs of the PA are generated during the various creation ceremonies. For this, only stand-alone computer systems are used. These computer systems are not connected to a network; all communication between systems takes place through media such as USB stick or smartcard. Because the generation and the use of the signing key of the PA takes place occasionally, the computer systems are only used for this purpose. For the majority of the time, the critical components of the computer systems are stored in a safe.
The signing keys of the G2 and above have the following key lengths:
TSP sub-CA certificates 4096 bit RSA keys
TSP certificates 4096 bit RSA keys
Domain certificates 4096 bit RSA keys
Root certificate 4096 bit RSA keys
6.2 Private Key Protection and Cryptographic Module Engineering Controls
6.3
The active signing keys of the PA are always located in the secure housing of a cryptographic module (HSM) which meets the following:
the requirements laid down in the standard FIPS PUB 140-2 level 3 or higher, or the requirements defined in standard CWA 14167-2, or;
a trustworthy system that (as a minimum) is certified in accordance with ISO 15408 at evaluation guarantee level EAL 4+ or equivalent security criteria.
All actions with the signing keys of the PA take place in accordance with pre-defined procedures. The persons who must be present when these actions are being performed are appointed beforehand. The signing keys of the PA can only be unlocked for use when these persons are present.
Under no circumstances are the signing keys of the PA passed on to a third party for storage.
If the signing keys are taken out of service at the end of the life time, for security reasons, these signing keys will not be archived. The signing keys are destroyed in an appropriate manner, to prevent them from being reused.
A back-up is produced of all signing keys. These back-ups are stored in a different location to the location where the operational signing keys are stored. The same security measures apply to both back-ups and operational signing keys.
6.4 Other Aspects of Key Pair Management
For certificates of the G2 hierarchy, the following term of validity applies:
TSP sub-CA certificates 12 years minus 3 days
TSP certificates 12 years minus 2 days
Staat der Nederlanden <Domain> CA – G2 12 year minus 1 day
Staat der Nederlanden Root CA – G2 12 years
As from the G3 hierarchy, the following term of validity applies:
TSP sub-CA certificates 15 years minus 3 days
TSP certificates 15 years minus 2 days
Staat der Nederlanden <Domain> CA –<Gen> 15 years minus 1 day
Staat der Nederlanden Root CA –<Gen> 15 years
In the hierarchies of the G3 and higher, the private keys of the Staat der Nederlanden Root and Domain CAs are used for no more than 6 years to issue TSP certificates. For the remaining 9 years of the term of validity of the relevant generation, the public key can be used to validate the underlying certificates.
Five years after creating a hierarchy, the next generation is created.
6.5 Activation data
Activation data for the information systems, such as passwords and PIN codes are, like the partial keys, stored in separate seal bags in the PKIoverheid safe.
6.6 Computer Security Controls
The computers of the PA used to perform actions with a signing key belonging to the PA can only be accessed by authorised members of staff. Software-based checks are incorporated in the systems, which are responsible for access control. The software checks the authorization of the staff member before the relevant actions can take place on the computer system. The actions performed on the computer systems are logged in such a way that, at a later stage, it can be ascertained which staff member performed the logged actions. The logs that are kept are verified periodically, at least annually, by the PA.
The computer systems of the PA referred to here are implemented in such a way that only the essential actions can be performed. All unnecessary components, such as additional software installed with the OS, are removed. The computer systems are stand-alone systems, therefore provisions relating to network security do not apply. Only the separate directory server for publishing the CRL and certificates is connected to a public network. This connection has extra security, in the form of a firewall.
Measures have also been taken to detect unauthorized attempts to access the systems in a timely manner.
The PA shall ensure that the cryptographic hardware and software used by the PA to sign certificates can never be modified unnoticed. This is monitored throughout the entire lifecycle of the cryptographic hardware and software.
6.7 Life Cycle Security Controls
The hardware and software used in the central hierarchy for the key management are classified by the NBV8at level ‘Confidential’. If any changes are made to the information systems, another evaluation is performed.
After extensive testing, CA systems are taken in production and maintained by the technical administrator. Software updates are carefully implemented after consultation with and in the presence of the PA PKIoverheid.
6.8 Network Security Controls
The Staat der Nederlanden Root CA is offline. The Staat der Nederlanden <Domain> CA is also offline. The CRLs described in this in CPS are provisioned online by means of the Certificate Status Service. The technical administrator of the Staat der Nederlanden Root CA of Logius has taken measures to safeguard the stability, the trustworthiness and the security of the network. This includes, for example, measures to regulate data traffic and to prevent unwanted data traffic, as well as the inclusion of firewalls in order to guarantee the integrity and exclusivity of the network. Measures have also been taken to detect unauthorized attempts to access the systems in a timely manner.
The Directory Service is part of the annual ETSI EN 319 411-1/2 audit. This is performed by an external IT auditor. In addition, every year the Directory Service undergoes a penetration test. This is carried out by an external IT security company.
6.9 Time-stamping
The PA does not support a timestamping service as part of its services.
6.10 Cryptographic algorithms (non RFC3647)
With trustworthiness of the PKI for the government in mind, a limited number of cryptographic algorithms are permitted within the PKI for the government. On a regular basis the PA shall check whether the standards that are applied still comply with ETSI TS 102 176-1, taking into consideration the anticipated developments. Should a switch to a different algorithm be necessary, the National Communications Security Agency (NBV-AIVD) will be asked for advice beforehand. Based on the ETSI standard, the certificate profiles included in part 3 of the Programme of Requirements state which algorithms are permitted.
7 Certificate and CRL profiles
7.1 Certificate Profile
Appendices C and D contain an overview of the content of the fields of the G2 and G3 root certificate and of the domain certificates.
7.2 CRL profiles
A CRL contains information about revoked certificates that fall within the current period of validity or of which the period of validity expired less than 6 months ago.
The CRLs comply with the X.509v2 standard for public key certificates and CRLs.
The CRL of the domain CAs is valid for one year. The CRL of the TSP CAs is valid for six months.
There is a transition period of two weeks before the CRL expires, in which a new CRL is published.
| Attribute | |
|---|---|
| Version | V2 Describes the version of the CRL profile. Value 1 represents X.509 version 2 CRL profile. |
| Provider | CN = Staat der Nederlanden Root CA - [version if applicable] O = Staat der Nederlanden C = NL |
| Effective date | Effective date of the CRL |
| Next update | The latest date on which an update can be expected, however an earlier update is possible. Contains the date and time on which the next version of the CRL is expected (at the latest). |
| Algorithm for the signature | sha256 The value is equal to the field signatureAlgorithm and contains the algorithm that is used for signing. The signing algorithm is SHA-256WithRSAEncryption. |
| Revocation list | Revoked certificates with the date of revocation. Includes the date and time of revocation and serialNumber of the revoked certificates. |
| CRL number | Sequential number of publication of the CRL in hexadecimal notation. |
7.3 OCSP profiles
The root CA and the domain CA ‘Organization Services’ use OCSP and OCSP signing certificates. OCSP signing certificates are valid for 14 months and are re-signed annually.
The OCSP responses and OCSPSigning certificates fulfil the requirements laid down in this respect in IETF RFC 2560. OCSPSigning certificates are in line with the X.509v3 standard for public key certificates.
| Basic Extensions | OID | Critical | Value |
|---|---|---|---|
| Certificate | N/A | ||
| SignatureAlgorithm | { pkcs-1 5 } | N/A | |
| Algorithm | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | ||
| SignatureValue | Signature by Staat der Nederlanden Root CA – G<number> | ||
| TBSCertificate | N/A | ||
| Version | 2 | ||
| serial number | SHA1 hash or public key generated by Staat der Nederlanden <Domain> CA – G<number> | ||
| Issuer DN | C=NL O=Staat der Nederlanden CN=Staat der Nederlanden Root CA – G<number> |
||
| Subject DN | C=NL O=Staat der Nederlanden CN=Staat der Nederlanden Root CA – G<number> OCSP Responder n (n= 1, 2, 3) |
||
| Validity | |||
| notBefore | dd-mm-yyyy (Date of the ceremony) | ||
| notAfter | dd-mm-yyyy (14 months after the date of the ceremony) | ||
| Public Key Algorithm | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | ||
| Public Key Length | 4096 | ||
| Standard Extensions | OID | Critical | Value |
| BasicConstraints | {id-ce 19} | TRUE | n/a |
| CA | Clear (FALSE) | ||
| pathLenConstraint | n/a | ||
| KeyUsage | {id-ce 15} | TRUE | n/a |
| digitalSignature | Set | ||
| CertificatePolicies | {id-ce 32} | FALSE | n/a |
| policyIdentifiers | 2.16.528.1.1003.1.2.1.1 (Root-CA_CP) | ||
| policyQualifiers | N/A | ||
| policyQualifierID | 1.3.6.1.5.5.7.2.1 | ||
| Qualifier | https://cps.pkioverheid.nl | ||
| policyQualifiers | n/a | ||
| policyQualifierID | 1.3.6.1.5.5.7.2.2 | ||
| Qualifier | The Certification Practice Statement of the PA PKIoverheid applies to this certificate, which can be consulted at https://cps.pkioverheid.nl | ||
| SubjectKeyIdentifier | {id-ce 14} | FALSE | n/a |
| KeyIdentifier | Method-1 | ||
| authorityKeyIdentifier | {id-ce 35} | FALSE | n/a |
| KeyIdentifier | Hash of public key of Issuing CA | ||
| CRLDistributionPoints | {id-ce 31} | FALSE | n/a |
| DistributionPoint | n/a | ||
| Full Name (URI) | http://crl.pkioverheid.nl/RootLatestCRL-G<nummer>.crl | ||
| extendedKeyUsage | {id-ce 37 } | TRUE | n/a |
| Key Purpose - OCSPsigning | {id-kp 9} | 1.3.6.1.5.5.7.3.9 | |
| PrivateExtensions | OID | Critical | Value |
| id-pkix-OCSP-nocheck | 1.3.6.1.5. 5.7.48.1.5 | FALSE | 05 00 (Null) |
8 Conformity assessment Compliance Audit and Other Assessment
8.1 Frequency and circumstances of the conformity assessment
The PA of PKIoverheid shall comply with the requirements described in the latest version of the WebTrust program for CA. To this end, the PA of PKIoverheid undergoes an annual WebTrust for CA Audit9.
Besides the Principles and Criteria for the Audit Criteria, the PA PKIoverheid also complies with the SSL Baseline Requirements Audit Criteria of WebTrust.
The PA PKIoverheid shall actively monitor the changes in the WebTrust program for CA that affect this CPS. The PA PKIoverheid will also actively monitor changes in the Baseline Requirements of the CA / Browser Forum that affect this CPS and the Programme of Requirements of PKIoverheid. The impact of these changes on the CPS and PoR of PKIoverheid shall be assessed.
The PA PKIoverheid also conforms with established government policy in relation to information security and privacy.
8.2 Identity, qualifications of the auditor
Audits are performed by an external certified WebTrust for CAs auditor.
8.3 Topics covered by the conformity assessment
This audit determines whether the quality and the security measures of the organization that has been set up meet the stipulated WebTrust standards.
8.4 Actions based on deviations
If additional security measures are recommended, the PA shall immediately take actions to implement these measures.
8.5 Communicating the results
Through a WebTrust seal, published yearly on the Logius website, the PA PKIoverheid demonstrates that it meets the WebTrust requirements.
8.6 Admittance of TSPs to the PKI for the government
See “part 2 of the Programme of Requirements PKIoverheid”10
9 Other Business and Legal Matters
9.1 Fees
The Staat der Nederlanden <Domain> CAs contain a reference to this CPS. No fee is charged for consulting these certificates or the information referred to. This applies to:
consulting the certificates;
consulting the revocation status information (CRLs);
consulting the Programme of Requirements: Certificate Policies and;
consulting this CPS.
9.2 Financial Responsibility
In terms of liability, the general rules of Dutch law apply with respect to the content and scope of the statutory obligation to pay compensation. The Ministry of the Interior and Kingdom Relations and a TSP enter into an agreement or contract concerning participation of the relevant TSP in the PKI for the government. In essence, this means that the TSP is obliged to provide services under the conditions stipulated by the Ministry of the Interior and Kingdom Relations, particularly the conditions laid down in the Programme of Requirements. In this respect, the PA is the point of contact for the TSP.
Provisions regarding the liability of the Ministry of the Interior and Kingdom Relations towards a TSP are included in an agreement or contract between the Ministry of the Interior and Kingdom Relations and the TSP. The requirements that the liability of the TSP must meet, are stated in the Programme of Requirements , part 3: Certificate Policies.
The TSP enters into agreements with subscribers and relying parties. Also laid down in these agreements is the liability of the TSP in respect of subscribers and relying parties. The requirements that this liability must meet are included in the General Provisions of the Programme of Requirements, part 3: Certificate Policies.
The Staat der Nederlanden has not taken out insurance for claims for compensation in respect of any liability.
9.3 Confidentiality of Business Information
The Policy Authority PKIoverheid handles company data confidentially. Only employees of the PA PKIoverheid have access to this data.
Company data, such as audit reports and Corrective Action Plans of TSPs will be encrypted before exchange will take place.
9.4 Confidentiality of Personal Information
Unlike the TSP, PA PKIoverheid does not issue certificates to natural persons. A register with the personal data of certificate holders is therefore not available.
9.5 Intellectual Property Rights
This CPS is the property of Logius. Unaltered copies of this CPS may be distributed and published without consent, provided that the source is quoted.
9.6 Representations and Warranties
See paragraph 9.2.
9.7 Disclaimers of Warranties
See paragraph 9.2.
9.8 Limitations of Liability
See paragraph 9.2.
9.9 Indemnities
See paragraph 9.2.
9.10 Term and Termination
This is version 4.0 of the "CERTIFICATION PRACTICE STATEMENT (CPS) Policy Authority PKIoverheid certificates to be issued by the Policy Authority of the PKI for the government", October 2016.
This CPS is valid as from the date of entry into force. The CPS is valid for the period of time that the services of the PKI for the government continue or until the CPS is replaced by a newer version. Newer versions are marked with a higher version number (vX.x). If substantial changes are made, the version number if increased by 1; if other less substantial changes are made, the version number is increased by 0.1. Newer versions are published on the following website (https://cps.pkioverheid.nl).
9.11 Individual notices and communications with participants
If TSPs have any questions, they can contact the PA PKIoverheid.
Regular communication takes place by email between the PA and the TSPs that participate in the PKIoverheid framework.
TSPs are immediately informed about the publication of a new version of the CPS or Programme of Requirements. Intended changes are also announced as soon as possible.
Besides communication with the TSPs, frequent contact also takes place with AT11and the auditor(s) of the participating TSPs.
9.12 Amendments
The Ministry of the Interior and Kingdom Relations is responsible for this CPS. The Ministry has delegated this task to Logius. This also includes the approval of changes to this CPS.
Any changes not considered to be changes of an editorial nature, are announced and result in a new version of the CPS. Changes of an editorial nature will not give rise to a new version of the CPS being published.
9.13 Dispute Resolution Provisions
Refer to the individual agreements between Logius PKIoverheid and TSPs.
9.14 Governing Law
Dutch law shall apply.
9.16 Compliance with Applicable Law
The PA function is performed by Logius. Logius is a digital government service and a division of the Directorate-General for Government organisations. The General Administrative Law Act12 applies to Logius.
Appendix A. Publication of Root Certificate announcement
9.17 Root certificate G2
As published in the Official Gazette (Staatscourant) dated Monday 15 December 2008 (no. 243, page 1).
Official publication
The Minister of the Interior and Kingdom Relations announces that, on the 26th of March 2008, a new root certificate of the PKI for the government has been created under the name
Staat der Nederlanden Root CA – G2 Certificate
This root certificate is the central part of the PKI for the government. The root certificate is the pivotal point for trust in electronic transactions from and with the government when establishing identity, indicating volition and communicating confidentially.
The root certificate holder is identified as Staat der Nederlanden Root CA – G2 (Common name), Staat der Nederlanden (Organization), NL (Country).
The serial number of the root certificate is 10000012 (hexadecimal 0098 968C).
The root certificate is valid until: Wednesday 25 March 2020 11h:03m:10s GMT.
The identification of the root certificate (the fingerprint in hexadecimal form) based on the SHA1 algorithm is: 59AF 8279 9186 C7B4 7507 CBCF 0357 46EB 04DD B716
This root certificate, the underlying documents related tothis certificate and further information about this root certificate are available in digital format on the website: http://www.pkioverheid.nl/. This website provides an explanation of how the root certificate can be identified.
The Policy Authority of the PKI for the government is responsible for managing the root certificate. This organization is part of Logius, the joint maintenance organization. Logius is part of the Ministry of the Interior and Kingdom Relations.
The Ministry of the Interior and Kingdom Relations,
G. ter Horst.
9.18 Root certificate G3
Official publication
The Minister of the Interior and Kingdom Relations announces that, on the 14th of November 2013, a new root certificate of the PKI for the government has been created under the name
Staat der Nederlanden Root CA - G3
This root certificate is the central part of the PKI for the government. The root certificate is the pivotal point for trust in electronic transactions from and with the government when establishing identity, indicating volition and communicating confidentially.
The root certificate holder is identified as Staat der Nederlanden Root CA – G3 (Common name), The State of the NetherlandsStaat der Nederlanden (Organization), NL (Country).
The serial number of the root certificate is 10003001 (hexadecimal 00 98 a2 39).
The root certificate is valid until: Tuesday 14 November 2028 0:00:00 hours.
The identification of the root certificate (the fingerprint in hexadecimal form) based on the SHA1 algorithm is: D8EB 6B41 5192 59E0 F3E7 8500 C03D B688 97c9 EEFC.
This root certificate, the underlying documents that support this certificate and further information about this root certificate are available in digital format on the website: http://www.logius.nl/producten/toegang/pkioverheid/. This website provides an explanation of how the root certificate can be identified.
The Policy Authority of the PKI for the government is responsible for managing the root certificate. This organization is part of Logius, digital government service of the Ministry of the Interior and Kingdom Relations.
The Minister of the Interior and Kingdom Relations.
10 Appendix B. Procedures for the change management of the PoR PKIoverheid
10.1 Consultation structure
Within the PKIoverheid framework the following bodies are involved in the change management of the Programme of Requirements: The PKIoverheid Change Council and PKIoverheid Framework Council.
The Framework Council comprises a delegation of the PA and the TSPs that participate in the PKIoverheid framework. The Change Council is also formed by a delegation of the PA and TSPs and the opportunity is given to invite experts.
Auditors of TSPs that participate in the PKIoverheid framework may join in the deliberations of the Change Council and/or Framework Council as a observer. When an auditor is present, he/she will have familiarised him/herself with the change proposals and is able to at least indicate whether a new or amended standard can be audited.
The specific aim of these bodies is facilitate consensus on changes to the Programme of Requirements (PoR).
The Change Council congregates to discuss draft change proposals and to reach, as far as possible, consensus on the final change proposals.
The Framework Council is a platform where announcements concerning the PKIoverheid framework by the PA are made and a proposed decision is taken on the inclusion of final change proposals in the next version of the PoR, including an effective date.
In principle, the Framework Council is convened twice a year in relation to the publication of a new version of the Programme of Requirements of PKIoverheid.
In any case, the Change Council meets one month before a Framework Council meeting, but can be convened more often in order to discuss change proposals which will have a significant impact.
Separate meeting are organised to discuss specific subjects, which are not directly related to current PoR changes.
10.2 Decision-making
During the Framework Council meeting, based on a consensus, an attempt is made to take a proposed decision concerning the content and effective date of changes to the Programme of Requirements.
Changes to the PoR are enforced by the Ministry of the Interior and Kingdom Relations, which as the owner has ultimate responsibility for the PKIoverheid framework and makes decisions about enforcing change proposals, sometimes through an accelerated change procedure. The PA provides the owner with advice in this regard.
Each proposed change that has been discussed by the Framework Council or as a result of the accelerated change procedure is submitted by the PA for approval to an official appointed by the Ministry of the Interior and Kingdom Relations, along with a recommendation from the PA and the opinion of the TSPs13.
In addition, the official appointed by the Ministry of the Interior and Kingdom Relations will be informed about change proposals that have (temporarily) been revoked.
If there is a disagreement with the TSPs on a change proposal, the decision will be justified by the official from the Ministry of the Interior and Kingdom Relations.
After approval is given by the official appointed by the Ministry of the Interior and Kingdom Relations, the change will be published by the PA on the website of Logius in a way that is clearly identifiable and uses comprehensible language; also stated is when the change shall take effect.
In addition, the PA informs the TSP contact persons and the party that submitted the change proposal electronically and/or in writing of the decision that has been taken.
If there is a new version of the PoR, prior to publication a formal signature is required by both the director of Logius and the official appointed by the Ministry of the Interior and Kingdom Relations. In the event of an accelerated change procedure, approval of changes by email will suffice.
The official appointed by the Ministry of the Interior and Kingdom Relations reserves the right to make changes to the PoR autonomously in the context of an (imminent) incident, emergency or crisis.
10.3 Framework of standards
TSPs must comply with the content and effective date of changes approved or published by the official appointed by the Ministry of the Interior and Kingdom Relations.
When a TSP cannot meet the effective date of a new or changed requirement, the TSP must ask for formal dispensation for this from the PA PKIoverheid.
A request for dispensation is formally submitted at the latest one week after the convening of the Framework Council and must be announced during the meeting.
Dispensation has to be requested electronically and/or in writing from the PA PKIoverheid.
The PA submits the proposed granting of dispensation for approval to the official appointed to that end by the Ministry of the Interior and Kingdom Relations.
The PA shall respond electronically and/or in writing stipulating whether the request is honoured or refused. The auditor of the TSP will receive a copy of this message.
10.4 Change proposals
The following parties can submit a change proposal regarding a part of, or a provision in the Programme of Requirements (PoR) through the usual or accelerated change procedure:
- The Ministry of the Interior and Kingdom Relations;
- the PA PKIoverheid (PA);
- CSPs within the PKI for the government that use the PoR.
The PA can submit change proposals based on the input from end users or other stakeholders. This will be clearly indicated in the change request.
Change requests are usually approved through by the Change Council and Framework Council. If a change cannot wait until the next version of the PoR, an accelerated change procedure can be followed.
A change proposal can be submitted by completing the request form "Change proposal Programme of Requirements" and sending this to the PA. This form can be found on the PA's website or can be requested directly from the PA.
The PA handles a submitted change proposal regarding a part of or a provision in the PoR in accordance with documented internal processes. In the event of a contentual change the PA will issue a recommendation, including text proposal, impact analysis (for a transitional arrangement, effective dates and possible dispensation, etc.) and reasoning. These are submitted to the TSPs for approval.
10.5 Ordinary change procedure
In principle, a new version of the PoR is published twice a year. A proposed decision regarding inclusion of a new or amended requirement in the PoR is taken during the meeting of the Framework Council prior to publication.
A change proposal is immediately distributed by the PA amongst the TSPs and the auditors of the TSPs as soon as a draft of the change is available.
Change proposals are sent to the TSPs at least ten weeks before the Framework Council meets.
Change requests submitted after this date will not be considered for publication in the next version of the PoR, unless the PA and TSPs agree unanimously that this change can still be included.
TSPs have five weeks to analyse change proposals and to give feedback to the PA.
This feedback is discussed during the Change Council meeting prior to the meeting of the Framework Council.
Taking the Change Council input into consideration, change proposals are finalised.
The PA sets the dates for the Change and Framework Council meetings. The meetings will take place as soon as possible after the latest draft proposals for the next version of the PoR have been distributed. There will be a minimum of 4 weeks between the Change Council meeting and the Framework Council meeting.
The final change proposals are sent to the TSPs and the auditors no later than two weeks after the Change Council meeting, along with the agenda for the Framework Council meeting.
The response time of TSPs to the agenda and the final change proposals is at least one week and endsno later than one week before the Framework Council meeting.
TSPs are expected not to put forward new insights once the final change proposals have been completed and distributed. This is meant to prevent the PA and other TSPs being forced to take a decision during the Framework Council meeting without the possibility to carefully consider the content of the new proposal.
If the delegation from a TSP cannot be present during a Change or Framework Council meeting, the TSP contact person is expected to elaborate on their point of view in advance and in writing concerning the content and the effective date of changes.
Following the Framework Council meeting, the PoR will be published as soon as possible.
The effective dates of changes are specifically included in the PoR.
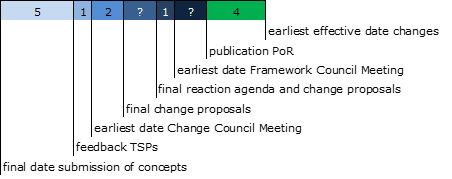
10.6 Accelerated change procedure
Changes are usually dealt with through the ordinary change procedure. In the event of an (imminent) incident, emergency or crisis, the official appointed by the Ministry of the Interior and Kingdom Relations can make changes autonomously. In addition, an accelerated change procedure can be followed, if it is necessary to enforce a change well before publication of a new version of the PoR.
Using the utmost caution the PA decides when it is necessary to follow an accelerated change procedure.
An accelerated change procedure entails the following process:
The TSPs, the auditors of the TSPs and the official appointed by the Ministry of the Interior and Kingdom Relations are informed by email of the intention of the PA to publish a change through an accelerated change procedure on the Logius website , along with the change request.
TSPs have at least one week to submit objections to the content and/or effective date of this change.
Any objections will be carefully considered by the PA PKIoverheid which, in close consultation, shall endeavour to provide sound advice.
The decision making process followed by the Ministry of the Interior and Kingdom Relations is described in the paragraph entitled “Decision-making”.
The PA publishes the change on the website and communicates this to the TSPs. The TSPs must adhere to the content and the effective date of the change published on the Logius website.
10.7 Miscellaneous
The PoR and the approved changes can be obtained in electronic form via the Internet on the PA's website: http://www.logius.nl/pkioverheid.
In the PoR, reference is made to this change procedure, which is included in the CPS of PKIoverheid.
11 Appendix C. Certificate profile TSP CA G3
| Basic Extensions | OID | Critical | Value |
|---|---|---|---|
| Certificate | N/A | ||
| SignatureAlgorithm.Algorithm | { pkcs-1 5 } | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | |
| SignatureValue | Signature by Domain <domainname> CA – G<number> generated | ||
| TBSCertificate | N/A | ||
| Version | 2 | ||
| SerialNumber | by Domain <domainname> CA – G<number>generated | ||
| Signature | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | ||
| Issuer.CountryName | C | NL | |
| Issuer.OrganisationName | O | Staat der Nederlanden | |
| Issuer.CommonName | CN | Staat der Nederlanden <domain name> CA – G<number> | |
| Validity.NotBefore | dd-mm-yyyy | ||
| Validity.NotAfter | dd-mm-yyyy | ||
| SubjectCountryName | C | NL | |
| Subject.OrganisationName | O | <TSP name> | |
| Subject.OrganisationIdentifier | <NTR number> or <Government Identification Number> number of TSP in accordance with syntax from paragraph 5.1.4 of ETSI EN 319 412-1 | ||
| Subject.CommonName | CN | <TSP name> PKIoverheid <domain name> CA – G<number> | |
| subjectPublicKeyInfo | Public key TSP-CA (Keylength=4096) | ||
| Standard Extensions | OID | Critical | Value |
| CertificatePolicies | {id-ce 32} | FALSE | N/A |
| policyIdentifier | See the relevant PoR parts for PolicyIdentifiers | ||
| PolicyQualifierID | 1.3.6.1.5.5.7.2.1 (id-qt-cps) | ||
| Qualifier | https://cps.pkioverheid.nl | ||
| KeyUsage | {id-ce 15} | TRUE | N/A |
| KeyCertSign | Set | ||
| CRLSign | Set | ||
| authorityKeyIdentifier | {id-ce 35} | FALSE | N/A |
| KeyIdentifier | 160-bit SHA-1 Hash value of the Domain <domain name>CA – G<number> | ||
| SubjectKeyIdentifier | {id-ce 14} | FALSE | N/A |
| KeyIdentifier | 160-bit SHA-1 Hash value of this TSP CA | ||
| AuthorityInfoAccess* | {id-pe 1} | FALSE | |
| See table below | |||
| CRLDistributionPoints | {id-ce 31} | FALSE | N/A |
| DistributionPoint.FullName | http://crl.pkioverheid.nl/Dom<domeinnaam>LatestCRL-G<nummer>.crl | ||
| ExtendedKeyUsage** | {id-ce 37 } | FALSE | N/A |
| See table below | |||
| BasicConstraints | {id-ce 19} | TRUE | N/A |
| CA | Set | ||
| PathLenConstraint | 0 | ||
| QcStatement2 | { id-qcs-pkixQCSyntax-v2 } | FALSE | 0.4.0.194121.1.2 (id-etsi-qcs-SemanticsId-Legal) |
accessMethod
Only for Server CA certificates and optionally for Services
| accessMethod* | 1.3.6.1.5.5.7.48.1 | OCSP | |
|---|---|---|---|
| accessLocation: URI* | http://domorganisatieservicesOCSP-g3.pkioverheid.nl | ||
| accessMethod | 1.3.6.1.5.5.48.2 | Certification Authority Issuer | |
| accessLocation: URI | http://cert.pkioverheid.nl/Dom<domeinnaam>CA–G<nummer>.cer |
Other CA Certificates
| accessMethod | 1.3.6.1.5.5.48.2 | Certification Authority Issuer | |
|---|---|---|---|
| accessLocation: URI | http://cert.pkioverheid.nl/Dom<domeinnaam>CA–G<nummer>.cer |
ExtendedKeyUsage
Only for Server CA certificates:
| Id-kp-serverAuth | {id-kp 1} | 1.3.6.1.5.5.7.3.1 | |
|---|---|---|---|
| Id-kp-clientAuth | {id-kp 2} | 1.3.6.1.5.5.7.3.2 | |
| Id-kp-OCSPsigning | {id-kp 9} | 1.3.6.1.5.5.7.3.9 |
Other CA certificates:
| Id-kp-clientAuth | {id-kp 2} | 1.3.6.1.5.5.7.3.2 | |
|---|---|---|---|
| Id-kp-Emailprotection | {id-kp 4} | 1.3.6.1.5.5.7.3.4 | |
| Id-kp-OCSPsigning | {id-kp 9} | 1.3.6.1.5.5.7.3.9 | |
| szOID_KP_DOCUMENT_SIGNING | 1.3.6.1.4.1.311.10.3.12 | ||
szOID_EFS_CRYPTO (Encrypting File System) |
1.3.6.1.4.1.311.10.3.4 |
12 Appendix D. Content fields G2 root certificates and domain certificates
| Att ribute | Root certificate | Organization Domain | Citizen Domain | Autonomous Devices Domain | |
|---|---|---|---|---|---|
| V ersion | V3 | ||||
| Serial number | 0098 968C | 0098 96F4 | 0098 96F3 | 0098 97BB | |
| Alg orithm for sig nature | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | ||||
| Pr ovider | CN = Staat der Nederlanden Root CA - G2 O = Staat der Nederlanden C = NL |
||||
| Valid f rom/to | Wednesday 26 March 2008 12:18:17 Wednesday 25 March 2020 12:03:10 |
Monday 31 March 2008 13:03:09 Tuesday 24 March 2020 14:02:08 |
Monday 31 March 2008 11:45:11 Tuesday 24 March 2020 12:43:57 |
Tuesday 3 November 2009 14:35:47 Tuesday 24 March 2020 14:34:41 |
|
| S ubject | CN = | Staat der Nederlanden Root CA - G2 | Staat der NederlandenStaat der Nederlanden OrganisatieCA - G2 | Staat der Nederlanden Burger CA - G2 | Staat der Nederlanden Autonome ApparatenCA - G2 |
| O = | O = Staat der Nederlanden | Staat der Nederlanden | Staat der Nederlanden | Staat der Nederlanden | |
| C = | NL | NL | NL | NL | |
| Public Key | RSA (4096 Bits) Concerns number series. Contains, among other things, the public key. | RSA (4096 Bits) Concerns number series. Contains, among other things, the public key. | RSA (4096 Bits) Concerns number series. Contains, among other things, the public key. | RSA (4096 Bits) Concerns number series. Contains, among other things, the public key. | |
| Certi ficate Po licies | ID=2.5.29.32.0 Policy qualification-ID=CPS <http ://www.pkioverheid.nl/p olicies/root-policy-G2> |
ID=2.5.29.32.0 Policy qualification-ID=CPS <http: //www.pkioverheid.nl/pol icies/dom-org-policy-G2> |
ID=2.5.29.32.0 Policy qualification-ID=CPS <http://www .pkioverheid.nl/polic ies/dom-bu-policy-G2> |
ID=2.5.29.32.0 Policy q ualification-ID=CPS <http://www.pki overheid.nl/policie s/dom-aa-policy-G2> |
|
| Key ID of CA | N/A | Key ID=91 68 32 87 15 1d 89 e2 b5 f1 ac 36 28 34 8d 0b 7c 62 88 eb Certificate provider: CN=Staat der Nederlanden Root CA - G2 O=Staat der Nederlanden C=NL Serial number of certificate=0098 968C |
|||
| CRL distri bution | N/A | URL= <http://crl.pkioverheid. nl/RootLatestCRL-G2.crl> | |||
| Key ID of s ubject | 91 68 32 87 15 1d 89 e2 b5 f1 ac 36 28 34 8d 0b 7c 62 88 eb | 39 10 8b 49 92 5c db 61 12 20 cd 49 9d 1a 8e da 9c 67 40 b9 | 91 a5 0d dd 1d a0 d1 2a 68 a7 1b 8d db 48 9a aa 34 a9 7f 96 | 7d 76 81 96 1e 4a 29 d1 ce 5e 12 0a 2a d4 d1 d4 ed bc ed 99 | |
| Ess ential const raints | Subjecttype=CA Constraint for path length=None |
||||
| Key usage | Certificate signing , Offline CRL signing, CRL signing(06) | ||||
| Finge rprint alg orithm | sha1 | ||||
| Finge rprint | 59AF 8279 9186 C7B4 7507 CBCF 0357 46EB 04DD B716 | 0B28 9953 4531 27C4 0B22 FA95 3D11 F79E 052C 0580 | 1F86 401F 89BB DE38 251A 718D E9E4 44EA 9936 EBE1 | EAFD 2EAB 7089 485D FDD2 8C4A CA1B 27F2 E34E 6717 |
13 Appendix F. Content fields G3 root certificates and domain certificates
| Attribute | Root certificate | Citizen Domain | Organization Services Domain | Organization Person Domain | Autonomous Devices Domain |
|---|---|---|---|---|---|
| Version | V3 | ||||
| Serial number | 00 98 a2 39 | 00 98 a2 47 | 00 98 a2 3c | 00 98 a2 46 | 00 98 a2 a0 |
| Algorithm for signature | sha256WithRSAEncryption (1.2.840.113549.1.1.11) | ||||
| Provider | CN = Staat der Nederlanden Root CA – G3 O = Staat der Nederlanden C = NL |
||||
| Valid from/to | Thursday 14 November 2013 12:28:42 Tuesday 14 November 2028 0:00:00 |
Thursday 14 November 2013 17:08:12 Monday 13 November 2028 0:00:00 |
Thursday 14 November 2013 13:27:56 Monday 13 November 2028 0:00:00 |
Thursday 14 November 2013 16:09:37 Monday 13 November 2028 0:00:00 |
Friday 15 November 2013 10:04:59 Monday 13 November 2028 0:00:00 |
| Subject CN = | Staat der Nederlanden Root CA – G3 | Staat der Nederlanden Burger CA - G3 | Staat der Nederlanden Organisatie Services CA - G3 | Staat der Nederlanden Organisatie PersoonCA - G3 | Staat der Nederlanden Autonome Apparaten CA - G3 |
| Subject O = | Staat der Nederlanden | Staat der Nederlanden | Staat der Nederlanden | Staat der Nederlanden | Staat der Nederlanden |
| Subejct C = | NL | NL | NL | NL | NL |
| Public Key | RSA (4096 Bits) | RSA (4096 Bits) | RSA (4096 Bits) | RSA (4096 Bits) | RSA (4096 Bits) |
| Certificate Policies | N/A | ID=2.16.528.1.1003.1.2.3.1 ID=2.16.528.1.1003.1.2.3.2 ID=2.16.528.1.1003.1.2.3.3 Policy qualification-id=CPS https://cps.pkioverheid.nl |
ID=2.16.528.1.1003.1.2.3.4 ID=2.16.528.1.1003.1.2.3.5 ID=2.16.528.1.1003.1.2.3.6 Policy qualification-id=CPS https://cps.pkioverheid.nl |
ID=2.16.528.1.1003.1.2.5.1 ID=2.16.528.1.1003.1.2.5.2 ID=2.16.528.1.1003.1.2.5.3 Policy qualification-id=CPS https://cps.pkioverheid.nl |
ID=2.16.528.1.1003.1.2.6.1 ID=2.16.528.1.1003.1.2.6.2 ID=2.16.528.1.1003.1.2.6.3 Policy qualification-id=CPS https://cps.pkioverheid.nl |
| Authority Key Identifier (AKI) | N/A | Key-ID=54 ad fa c7 92 57 ae ca 35 9c 2e 12 fb e4 ba 5d 20 dc 94 57 | |||
| CRL distribution | N/A | URL= http://crl.pkioverheid.nl/RootLatestCRL-G3.crl | |||
| Subject Key Identifier (SKI) | 54 ad fa c7 92 57 ae ca 35 9c 2e 12 fb e4 ba 5d 20 dc 94 57 | ff 68 75 42 7d fa 6f c7 5a 93 38 9f 35 44 d0 aa 2d 00 b2 89 | 43 eb 4d 00 d3 95 93 ce a6 7c 40 0d 6d 11 be 39 d1 32 ae e2 | ee ac 6d 40 ea d5 04 6a 87 2c 55 7b f5 3f 2d da ee db ac e2] | 6d 1b 25 02 5d e0 48 f4 6e 13 75 e2 57 84 9d 50 f3 30 14 43 |
| Authority Information Access | N/A | N/A | OCSPURI=http://rootOCSP-g3.pkioverheid.nl | N/A | N/A |
| Basic constraints | Critical -CA:TRUE |
||||
| Key usage | Critical
|
||||
| Fingerprint algorithm | SHA256 | SHA256 | SHA256 | SHA256 | SHA256 |
| Fingerprint | 3C 4F B0 B9 5A B8 B3 00 32 F4 32 B8 6F 53 5F E1 72 C1 85 D0 FD 39 86 58 37 CF 36 18 7F A6 F4 28 | 2E 7A 0A 3B 0C 52 7E B2 0C 52 25 3C 8D 22 78 CA 10 81 36 A8 CA 3A 4E A2 2D A7 B5 9B AC 90 65 0A | D9 58 1D BD E9 9B 39 EE FF 6C E5 C8 0D E1 65 0D A0 C1 C8 A1 09 70 5E D2 86 C5 3B C9 5E 66 55 E4 | 82 22 BC 4F E7 A3 DD CA 9E F0 BF 0D 68 2A C8 88 79 9F 87 82 2D 15 33 2A 54 C0 BF DF C6 85 4F 7B | AD 49 3D 6E 85 EC 60 8A B8 13 A8 87 BD C4 D4 19 6A 0B C9 B3 3D 25 65 A7 FA 8A C4 30 F0 8A 99 A5 |
See in this respect the paper “De Elektronische Overheid aan het begin van de 21e eeuw” (House of Representatives, session Lower House 2000-2001, 26 387, no. 9) by the Minister for Major Cities - and Integration Policies to the President of the House of Representatives of the States - General.↩︎
For more information regarding abbreviations, refer to the Programme of Requirements PKIoverheid section 4: definitions and abbreviations (https://www.logius.nl/ondersteuning/pkioverheid/aansluiten-als-TSP/programma-van-eisen/)↩︎
The central part concerns Staat der Nederlanden Root CA and Staat der Nederlanden <domain> CAs.↩︎
These checks are usually performed automatically by the application that is used. The aforementioned checks have to be performed for every certificate in the chain of trust.↩︎
For reasons of confidentiality, this CPS does not state between how many key holders the activation data are distributed.↩︎
Netherlands National Communications Security Agency (Nationaal Bureau voor Verbindingsbeveiliging)↩︎
https://www.logius.nl/ondersteuning/pkioverheid/aansluiten-als-TSP/programma-van-eisen/↩︎
Radiocommunications Agency. See also https://www.agentschaptelecom.nl/onderwerpen/zakelijk-gebruik/eidas-elektronische-vertrouwensdiensten/trust-service-providers↩︎
https://www.rijksoverheid.nl/documenten/besluiten/2006/06/21/engelse-tekst-awb↩︎
Currently, this is the director of the directorate for Information Society and Government from the Ministry of the Interior and Kingdom Relations.↩︎

